Non-profit organizations are enhancing their revenue streams through online platforms, necessitating robust cybersecurity measures to protect sensitive donor and financial data. Confidential Computing is a pivotal tool in this area, providing end-to-end encryption for secure online shopping experiences for high-net-worth individuals by safeguarding their transactions against cyber threats. This technology ensures that confidential information can be shared with partners or service providers without compromising privacy through multi-party computation. By prioritizing data protection and compliance with regulatory standards, non-profits are able to foster trust in digital giving platforms, which is essential for maintaining the integrity of relationships with high-net-worth donors and encouraging secure online contributions. Confidential Computing automates compliance checks, reducing administrative overhead while ensuring the highest level of security. Its deployment underlines a non-profit's commitment to secure online shopping practices, protecting against data breaches and upholding the privacy and integrity of donations in the digital age. As the expectation for secure handling of financial contributions grows, Confidential Computing stands out as a foundational element for trust in philanthropic transactions online.
Non-profit organizations are increasingly reliant on digital platforms to conduct transactions, engage with supporters, and manage donor information. In an era where cybersecurity threats loom large, the integrity and confidentiality of these operations are paramount. Confidential Computing emerges as a pivotal solution in safeguarding sensitive data during non-profit transactions. This article delves into the essentials of Confidential Computing, its critical role in secure online donations and fundraising, and actionable steps for implementing robust confidential computing solutions tailored for high-net-worth individuals’ online shopping experiences. By embracing these practices, non-profits can fortify their data privacy measures and foster a culture of trust among stakeholders.
- Understanding Confidential Computing: Ensuring Data Privacy for Non-Profit Transactions
- The Role of Confidential Computing in Secure Online Donations and Fundraising
- Implementing Confidential Computing Solutions to Protect High-Net-Worth Donor Information
- Best Practices for Non-Profits to Adopt Confidential Computing in their Operations
Understanding Confidential Computing: Ensuring Data Privacy for Non-Profit Transactions

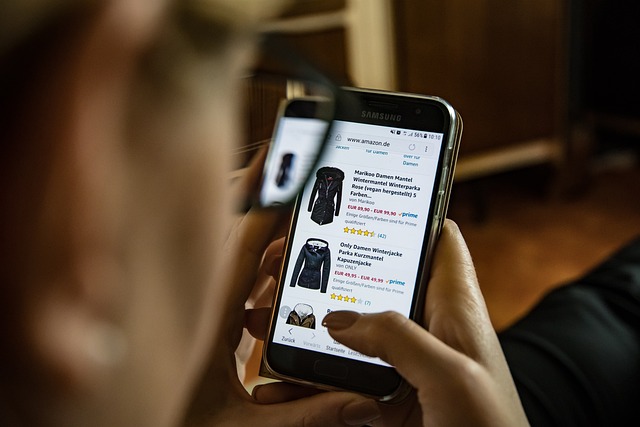
Non-profit organizations, much like their for-profit counterparts, are increasingly engaging in online transactions to diversify their revenue streams and reach a wider audience. As these entities often handle sensitive donor information and financial data, it is paramount to implement robust security measures to safeguard this data from unauthorized access and breaches. Confidential Computing emerges as a pivotal solution in this domain, offering a layer of encryption that protects data both at rest and in use. This ensures that high-net-worth individuals who contribute to these organizations can trust that their contributions are processed through secure online shopping systems, which are shielded from potential cyber threats.
In the realm of Confidential Computing, multi-party computation allows for the collaboration between entities without exposing the underlying data. For non-profits, this means they can share necessary donor information with partners or service providers while maintaining confidentiality. This approach is particularly valuable for high-net-worth individuals who are concerned about the privacy and security of their transactions and personal details. By adopting Confidential Computing, non-profits can reassure donors that their sensitive data will remain private throughout all online interactions, thereby fostering a secure environment for digital giving. This not only protects individual privacy but also upholds the trust between donors and the organizations they support.
The Role of Confidential Computing in Secure Online Donations and Fundraising

In an era where digital transformation is paramount, non-profit organizations are increasingly leveraging online platforms for fundraising and donations. The role of confidential computing in this domain is pivotal, as it ensures the sensitive financial data exchanged during online transactions remains private and secure. This technology provides a robust framework for encrypting data both at rest and in use, critical for safeguarding donor information against unauthorized access. For high-net-worth individuals who are inclined to contribute substantial amounts via digital means, the assurance of confidential computing makes online giving not only convenient but also secure, fostering trust and encouraging larger donations. The encryption and isolation techniques employed by confidential computing mitigate risks associated with data breaches, ensuring that personal and financial details associated with donations are protected at every step of the transaction process. This level of security is essential for maintaining donor confidence and trust, which are the cornerstones of sustained philanthropic support in the digital age.
Moreover, as non-profits navigate the complexities of online fundraising, they must also adhere to stringent regulatory compliance standards. Confidential computing aids in this aspect by automating compliance checks, thus reducing the administrative burden on these organizations. By integrating confidential computing solutions, non-profits can offer high-net-worth individuals a secure and reliable avenue for online donations, which aligns with the best practices of secure online shopping. This not only enhances the overall donor experience but also positions non-profit organizations as responsible and trustworthy entities in the digital space.
Implementing Confidential Computing Solutions to Protect High-Net-Worth Donor Information

Non-profits that manage contributions from high-net-worth donors must prioritize the security and confidentiality of sensitive financial information. With the rise of digital transactions, ensuring secure online shopping experiences for these individuals is paramount. Confidential Computing solutions emerge as a robust defense mechanism against data breaches and unauthorized access. By leveraging encryption technologies that extend beyond rest to encompass compute operations, non-profits can protect donor information throughout its lifecycle, from donation initiation to final transaction processing. This level of security not only upholds the trust between donors and organizations but also aligns with regulatory compliance standards, safeguarding against potential legal and reputational risks. Implementing Confidential Computing in the non-profit sector is a strategic investment that assures donors their financial contributions are handled with the highest degree of privacy and security, thereby facilitating an environment of trust and integrity for all online philanthropic activities. As high-net-worth individuals increasingly demand stringent data protection measures, Confidential Computing stands as a testament to a non-profit’s commitment to donor confidentiality and financial transparency.
Best Practices for Non-Profits to Adopt Confidential Computing in their Operations

Non-profits increasingly rely on online platforms to solicit donations and manage contributions from high-net-worth individuals, making data security a paramount concern. To safeguard sensitive donor information and maintain trust, non-profits must adopt robust security measures such as confidential computing. Confidential computing ensures that data processing occurs in a trusted execution environment, where both the compute instance’s code and its data are encrypted. This approach provides an additional layer of protection against potential breaches or unauthorized access.
For non-profits, especially those facilitating secure online shopping experiences for high-net-worth individuals, implementing confidential computing best practices is essential. These practices include a thorough assessment of the current IT infrastructure to identify areas that require encryption and secure multi-party computation capabilities. Non-profits should also establish clear data governance policies that dictate how data is handled within these confidential environments. Additionally, they should leverage cloud providers that offer confidential computing services specifically designed for sensitive workloads. By prioritizing the encryption of both code and data, non-profits can significantly reduce the risk of data leaks or unauthorized access, ensuring the integrity and privacy of their operations and maintaining the confidence of their donor base. It is crucial for these organizations to stay abreast of technological advancements in confidential computing to protect the financial contributions and personal information entrusted to them by high-net-worth individuals.
In conclusion, confidential computing presents a robust solution for non-profits to safeguard sensitive data, particularly in the realm of online donations and fundraising. By adopting this technology, organizations can protect the privacy of high-net-worth donors, ensuring secure online transactions that instill confidence and trust. The best practices outlined in this article serve as a guide for non-profits to implement confidential computing effectively, thereby mitigating risks and upholding their commitment to data protection. As non-profits increasingly rely on digital platforms for revenue, embracing confidential computing becomes not just a strategic move but an imperative for maintaining the integrity of their operations and honoring the trust placed in them by supporters. It is a step towards a future where online giving is both convenient and secure, ensuring that philanthropy can thrive in the digital age without compromising on privacy or security.